Dept. of Nested Tomfoolery
Thirty-odd years ago, on my “study tour” of the Soviet Union, a common souvenir was a political matryoshka doll of nested Soviet leaders. The sellers would call them “Gorbydolls”, since Gorbachev, who led the USSR from 1985 to 1991, was the current and thus outermost figure.
The most common variety went from Gorby directly to Brezhnev, then Khrushchev, then Stalin, and then Lenin — but savvy students of history (well, back then it was current events) knew that two men served as General Secretary between them.
Brezhnev looms large in Soviet history, since he led the country for longer than anyone other than Stalin: a bit over 18 years, from 1964 until 1982. The first forgotten man was Yuri Andropov, who held the means of production for only about 15 months from November ’82 through February ’84.
The Supreme Soviet then tapped Konstantin Chernenko, who had even worse luck: February of ’84 until March of ’85.
Only THEN did wGorby come to power.
I had an opportunity to get an actual correct doll in Moscow, but I didn’t clock to how rare they’d be, and as it was the first stop on the tour I demurred to avoid toting it for the rest of the trip. More fool me, though, as I never saw another correct example. (I did please a number of black marketeers by even KNOWING about the two missing leaders, though, which was fun.)
Anyway, years later, my pal Lindsey went over, and brought me an updated doll. Sadly, this one’s missing the short timers, too, but it has something else to amuse: it’s two-sided, with the Russian leaders on one side paired with American ones on the other. I had entirely forgotten this aspect of it until I took it off the shelf it’s lived on for 20+ years ahead of our big move.
Sounds fun, right? And it starts reasonably enough, unless you scratch the surface: It’s Putin on one side and Clinton on the other.
Except Clinton was done by January of 2001, whereas Putin took over in May of ’00, and remains in charge. OTOH, they were both “current” at the time, and so get the outer position. Fine.
But let’s look at doll #2: Boris Yeltsin and George H. W. Bush. Yeltsin led from 1991 until 1999; Bush was in office, famously, for only a single term ending in January of 1993. But they were contemporaries, at least for a time, so this makes some sense.
Moving on, at Doll #3, we find Gorby and Reagan. Here we have the strongest correlation, since Reagan served from ’81 to ’89, while Gorby was in office from ’85 to ’91. And, famously, Reagan addressed Gorby in his famous “tear down this wall” speech, so they’re historically linked.
Now we revert to form, as Doll #4 is Brezhnev (who led from ’64 to ’82) and Nixon (’69 to ’74). Sure, pairing an 18 year leader with a disgraced 5-year-man is questionable, but OTOH you gotta pick SOMEONE, right? (I might’ve picked Johnson.)
Doll #5 probably makes the most sense since Reagan and Gorby: it’s Khrushchev (’53 to ’64) and Kennedy (’61 to ’63).
Now we go OFF THE RAILS, though, because Doll #6 is necessarily Stalin. Stalin led the Soviet Union from 1924 until 1953; to borrow a phrase from a popular musical, no one else looms quite as large. So whom did the doll designers pick for the American side? You guessed it! Abraham Lincoln, US President from 1861 to 1865.
Doll #7 gives us a very, very tiny V. I. Lenin, who despite his iconic status led the USSR for only a year and 22 days (December of ’22 through January of ’24). That’s less time than either of the forgotten early-80s men. But: founder, so obviously on the tiny American side we find a very small face I presume to be George Washington (1789 – 1797).
POSTSCRIPT: It is only in writing this post that I discovered another forgotten man in the Soviet list: in fact, the Soviet leadership didn’t go directly from Stalin to Khrushchev. Georgy Malenkov held power for like half a year, but things were messier then.
Wheeee!
Banks are Parasites
Oh, banks.
We recently paid off our house. This triggers the lender — Chase — sending us the balance of our escrow account, which they sent me by check.
This is weird, because I also bank at Chase. I can see my accounts and my (former) mortgage in the same web UI.
I darkly thought, upon opening the envelope, that the whole reason it came as a check was to allow Chase to hold the money longer. Surely not, right?
Yeah, turns out? I deposited the check yesterday, and Chase is now telling me the funds are “on hold” until the 20th.
A check drawn from their own accounts, at the same bank.
Banks are parasites.
Anderson Evaluation Redux (2025 Edition)
In 2023, after being disappointed by ASTEROID CITY, I wrote this post wherein I ranked Andersons’ films.
Last night we saw THE PHOENICIAN SCHEME, which is a reasonable time to publish an amended list; n.b. the only edit is the insertion of the new film between Dogs and Rocket:
- Moonrise Kingdom (2012)
- Rushmore (1998)
- The French Dispatch (2021)
- The Royal Tenenbaums (2001)
- Fantastic Mr. Fox (2009)
- Isle of Dogs (2018)
- The Phoenician Scheme (2025)
- Bottle Rocket (1996)
- Grand Budapest Hotel (2014)
- The Life Aquatic with Steve Zissou (2004)
- Asteroid City (2023)
- The Darjeeling Limited (2007)
Mostly, the last two outings have just made me want to watch other films of his again (e.g., anything in the top half of the list).
One Weird Streak
Billy Joel had a hit in 1980 with “You May Be Right,” and shortly thereafter I bought my very first music: a copy of Glass Houses on 8-track.
In the last 45 years, I’ve bought a LOT of other music — a few others on 8-Track, a bunch on cassette, and then starting in 1988, a WHOLE LOT on CD. I didn’t start buying vinyl until about 20 years ago, and since that coincided with DRM-free digital and then all-you-can-eat streaming, vinyl collecting never reached the fever pitch of CD buying.
In all that time, though, the transaction was only ever “music to me, money to record shop.” There’s been attrition and loss, but I never sold anything.
Some of my college pals would occasionally sell one-hit wonder CDs or whatever, either because they didn’t want them cluttering up the collection or (more often) because they needed money. I never did, though. I still own award-worthy CDs like the second Blow Monkeys release, from 1986 (2.5 stars at Allmusic!). Whatever pittance the local shop would’ve given me for it wasn’t sufficient to forever lose the opportunity to hear “Diggin’ Your Scene” again, at least back in those scarcity-driven days.
I say “I never,” but of course the point of this message is that it was only “I never” until about 20 minutes ago, because I accepted $155 from Cactus for the culls from our vinyl collection.
It’s not that I don’t want to have those, and it’s not that we need the money; it’s that I don’t want to pay Mayflower to MOVE them.
Having received our first pack-and-move quotes, we are getting MUCH more aggressive about the pre-move purge.
And so: sic transit gloria mundi, eh?
The Past: Just a bit more Past today
Back in 2011, I noted here the surprising fact that 10th US President John Tyler (a man born in 1790) had two living grandchildren: Lyon Tyler, Jr. (b. 1924), and Harrison Ruffin Tyler (b. 1928).
This is, of course, only possible because President Tyler had many children between two wives; his oldest schild was born in 1815, but his youngest wasn’t born until 1860. The surviving grandchildren are sons of Lyon Gardiner Tyler, his fifth child from his second wife. Lyon Sr. was born in 1853 — when Tyler the elder was about 63.
Further, Lyon Sr. had these surviving sons quite late as well: he was about 71 and 73 for their arrivals. But that’s the kind of age spread you need to have living people with grandfathers born during the Washington Administration.
Lyon Jr. sadly passed away only about a year after that post, and just now I read that Harrison died this past weekend at the age of 96.
Over at Kottke’s site, he has a page devoted to The Great Span — cases where the scale of consecutive human lives put us in closer mental proximity to the events of the past (like, say, when we realize Tyler still had living grandchildren until last week). It’s a good read. On post, about The Betty White Timeline of Human History, discusses how far back certain events were using White’s lifetime (99 years) as a unit. For example, the fall of the Roman Empire was only 16 Bettys ago. We’ve only been writing for about 52 Bettys.
This same page points out the story of Daniel Smith, a DC area man who was the son of a slave and yet was profiled in the Washington Post in 2020.
Yes, the rumors are TRUE
We’re leaving Houston. For me, it’s after 31 years. For Erin, it’s “only” 23. But who’s counting?
Many of you knew this was something we were considering; in truth, it’s been an idea for about 4 years after a vacation in New Mexico, when the idea of “shit, we could live out here!” took root. After all, my job is portable and Erin’s skillset is marketable.
Then the climate really started to wear on us — Houston’s always been hot, but it feels like the last several summers have been even more brutal than ever. And then Governor Hotwheels and his cronies started being stupidly punitive towards Harris County’s big blue dot, and the confluence of political climate plus ACTUAL climate came to a head for us. And we started saving searches on Zillow.
- But I hear you’re not even GOING to New Mexico!
- TRUE! Turns out, the whole of the west is going to have a serious water crunch in the coming years, and we figure trading Houston’s flooding for its opposite wasn’t the best play. So we thought about other places.
- Like where?
- Well, California was on the list for a while, but living near friends in SoCal would involve a drastic rejiggering of household budgets. Seems like living well out there means spending WAY more of your money on real estate than we’re used to in plain ol’ Houston, and so we dismissed the idea (despite how attractive it is).
- So not Cali. Fine. What else?
- The Pacific Northwest is LOVELY, and we know some folks out there, and the climate absolutely agrees with us, but there are some issues that made it ultimately a nonstarter.
- PNW DQ, Pt 1.
- The PNW is, not to put too fine a point on it, kinda at the other end of the melting-pot diversity stick from Houston. Houston’s diversity has all sorts of benefits, not the least of which being “meeting different sorts of people is good for you.” Kidding on the square, though, a massive influx of immigrants from every corner of the globe is how Houston became an insanely good food town. You’re not gonna get that in a place without similar levels of inbound immigration.
- PNW DQ, Pt 2
- My mom’s 85 next month. Erin’s mom is 75 this year. All her family is in Florida; my sister is in Philly, and my mom is in Jackson, Mississippi. Going that far away started to feel unwise.
- And then: the epiphany
- Moving somewhere random at 25 is scary, sure, but at 25 finding your people is easy because all the other 25 year olds are ALSO trying to find their people. We have no illusions about our middle-aged status; the other 55 year olds are in bed by 9. It therefore occurred to us that picking a place where we already knew a ton of folks would probably be smart.
- Enter Durham
- Longtime Heathen Co-Conspirator MAD has lived in the area since the 20th century. He’s been low-key trying to get us up there for a while, and he’s not our only pal there. Turns out, our Crimson alma mater spat out no small number of seeds who took root in Tarheel country — two of Erin’s college roomies are in the area. At least a couple former members from the honors dorm I lived in are there. A pal or two from the English department and the literary magazine I helped found in 1990 are there, too. And, wouldn’t you know it, there’s at least one or two folks from my hometown there, and they’re in the set of “hometown people” I wouldn’t mind seeing again.
- Aren’t you leaving someone out?
- Yup. See, I moved to Houston in 1994 after having attended a friend of a friend’s birthday party here that summer, at Eric’s urging. Thomas became a friend of mine, too; his girlfriend at the time was actually one of my first roommates here. They eventually moved to Austin, married, and now have three kids. Oh, and last August? They moved to Raleigh. I can’t tell if that’s a Sign or a Portent, but it’s definitely one of them.
- But Durham’s in NC, and NC was red last time!
- True, but Durham itself is far bluer than Houston, and North Carolina is a state that’s legitimately purple. Texas, god bless her, only has aspirations of purpleness.
- What else?
- CLIMATE. Yes, Durham is still the south, and it will get warm there, but not Houston warm. (I mean, they THINK it’s hot, but they’re adorable. They’re also adorable when they talk about traffic.) They have actual seasons, but none of them are trying to kill you (vs summer in 713, or winter in the midwest). The humidity gap alone is enormous. We flew home yesterday, and the temperatures were about the same there and here — but there was a 22 point difference in humidity.
- There’s more.
- Currently, it’s 81F feeling like 89 in Houston; in Durham, it’s 74, and feels like 71.
- Sure, Chet, but it’s springtime! It’s nice everywhere.
- Fine. The real proof is summer. In August of 2024, Houston was over 90F all but 5 days, and over 95F for all but 9 days. Houston dipped below 80F at night only once before the final week of the month, and at NO POINT in August was the nighttime temp low enough to cool off by opening windows. In the same month, Durham was mostly topping out in the 80s, and regularly dipped into the 60s at night — and had a low of 55F on the 22nd.
- They have real winter there, Chet! Look out!
- Yes, it does get colder there. But it’s not like midwest cold. It’s more like a winter happens, and you might need to wear a sweater or a coat. Fine! It’s also not unremitting, like our summers; even in January, Durham had 13 days over 50F, which is hardly a frozen hellscape. OTOH, I could’ve worn shorts to a Christmas Eve party this year in Houston, which seriously harshes my yuletide glow.
- It still seems sudden!
- I mean, you’re not entirely wrong. We’ve been house shopping via Zillow for about a year, and we’ve been open about our desire to go, but I honestly think most of you didn’t take us seriously. And the logistics of selling and buying in a coordinated way kinda gobsmacked us. The market’s behavior means liquidating investments to afford a down payment against a house there WITHOUT selling our Houston home first seems really dumb. So we were stuck. How do people who aren’t rich even DO this?
- What changed?
- We realized our Houston place is close enough to being paid off that we could just pay it off, and then rent a place in Durham while we sell Houston. And that allowed things to accelerate pretty quickly.
- How quickly?
- Well, last weekend we were in Durham looking at rental contenders. We’re about 2 shakes from executing a lease on one of them that’s literally walking distance from the aforementioned Agent MAD and his Librarian Emeritus partner — both of whom have been dear friends of ours since the late 1980s. If this goes through, it’ll start on 6/15, and we’ll plan to be in Durham on or about 7/1.
- ZOMG!
- Yeah, I know.
- So can we get drinks / coffee / dinner / play a game / eat enchiladas?
- You’re goddamn right. Call me.
I legitimately AM freaking out a little. Houston has been my home for my entire adult life. I moved here in 1994. I had no idea it would worm its humid, verdant way into my heart so completely and for so long. I always had intentions of living many places, and now I’ve spent more than half my life in the one I picked on a whim when I was too young to rent a car. I’ve lived in the home I bought at age 30 longer than I ever lived anywhere else, and it’s not close AT ALL. (Statistically, it’s entirely possible I’ll never live anywhere this long again — 25 more years puts me at 80.)
I’m wigging out, a little. But the Houston I loved is changing, too. We’re not the only ones on the way out the door in our social circle, so even if we stayed it wouldn’t be the same city. And the summer would still piss me off more every year.
So yeah, we’re leaving. But we love you all, and that part won’t change.
In re: LANDMAN
It’s TV mogul Taylor Sheridan‘s latest project — he of YELLOWSTONE, of course, but also a few pretty good films. This time, instead of a grizzled and wise middle-aged dude played by Kevin Costner, our central character is a grizzled and wise middle-aged-dude played by Billy Bob Thornton.
Trouble is, I like Thornton. So I watched all 10 episodes on business travel this week.
It was absolutely a hatewatch.
First, it’s chock full of Taylor Sheridan’s standard validation of reactionary politics by only rebutting basic or simplistic arguments to the contrary. In YELLOWSTONE, it was about conservation efforts other than whatever John Dutton wanted. Here, it’s anything suggesting oil isn’t Right and Just. It’s not that Sheridan is dumb; I’m sure he knows better. It’s craven pandering to an audience that eats this stuff up as validation for their OWN points of view.
Second, it’s grotesquely misogynistic, which is again a Sheridan tradition. There are no fully realized female characters in anything he writes, even in stories notionally centered on women like his films WIND RIVER and SICARIO. His on-and-off-again ex-wife Angela and their daughter Ainsley (a carbon copy of her hypersexual mother) are awful, awful people. Rebecca Falcone, a lawyer brought in after an accident, is a thin Big City Person who must be taught how Things Really Are by the Wise Landman Who Knows Things.
Third, it’s absurdly full of middled-aged-man wish fulfillment. A broken down landman stands up to the cartel! His daughter actually listens to his Sage Advice! He’s rewarded with a promotion for helping to cover up how mismanaged the company’s wells and infrastructure are. He acts like an asshole to everyone around him, but suffers no interpersonal or professional consequences for it. Even the fucking CARTEL boss (and I’m still mad about how wasted Andy Garcia was here) is like “our bad, respect.”
BUT
Goddamn if Thornton isn’t fun to watch. I mean, he’s been fun to watch since SLING BLADE, but he was born to play Tommy.
Ali Larter — whom GenX folks will recall first came to fame as the fictional “it girl” Allegra Coleman in a satiric front-page celeb faux-profile in Esquire back in 1996 — makes an absolute meal of a thin, unbelievable character in ex-wife Angela. I don’t know if I’ve ever seen someone do so well with so little.
Jon Hamm, I think we probably all agree, seems unable to do wrong, and he’s not wrong here as the billionaire owner of the oil company in question. Having Demi Moore as his wife was genius, and while she’s not given much to do she does well doing it.
The supporting roles are generally great, too. I’d single out first Colm Feore as Nate, especially reacting to Ainsley’s antics and also just generally being the guy who gets to react like an actual person in most scenes.
Multi-project Sheridan company member James Jordan is having a HOOT as petroleum engineer Dale. We’ve seen him before as the main bad guy in WIND RIVER, and then again in MAYOR OF KINGSTOWN, and again in 1883, and again as Hendon on YELLOWSTONE, and again in LIONESS as Two Cups, and again in THOSE WHO WISH ME DEAD as Ben. (He, like Sheridan, had a small part on VERONICA MARS, so I reckon that was their initial connection.)
Jacob Lofland as Tommy’s son Cooper doesn’t have much to do early on, but really comes into his own in quiet scenes with Ariana, and in what comes after. However, the writing hurts him — we don’t really see anything at all that suggests he and Ainsley are related, even when they have brief scenes together. It seems obvious he’ll have a bigger role in S2.
Which is where I admit that yeah, I’ll probably hatewatch S2, too.
A couple notes that didn’t fit elsewhere
- Luring us in with Michael Pena as a seemingly central character that is immediately killed off is some dirty pool.
- Sheridan is weirdly obsessed with breastfeeding.
Dear Bosch: Die in a Fire
Holy shit this is incredibly stupid.
tl;dr: Brand new Bosch dishwasher required an app and a cloud service to run a rinse cycle. WTF?
The best movie I’ve seen this year
Granted, it’s March, but it also seems unlikely anything else I see in 2025 will top Hundreds of Beavers.
The argument is this: a wastrel applejack maker has a reversal of fortune and must survive the Wisconsin woods in winter. It is, above all, a cartoon — but a live action one. It’s not silent, but it has no dialog — eidetic sounds abound; characters grunt or otherwise erupt in exclamatory noises. The visual language is rich and consistent. The film’s look is a perfect hybrid of real and unreal, and the filmmakers achieved this miracle for about $150,000. Thus far, it’s made more than 10x that number.
Our hero must eat to survive, obviously, so his initial challenge is to trap a rabbit. The rabbits and all other animals in the story are represented by people in animal costumes; the viewer accepts this immediately.
There’s a tremendous amount of Warner Brothers vibe here, but also Buster Keaton and the Three Stooges. It’s wry and hilarious and smart, but it achieves this without spoken language. There’s a love interest, a protective father, a video-game worthy progression towards a goal, and deeply hilarious revelations about the state of the beaver scientific knowledge.
Absolutely four stars. My god, what a treat.
An interview with the director is here, and worth your time, but maybe watch it first. The film is apparently available at Amazon, Apple, and Tubi. However, we got to see it on the big screen last night over at the River Oaks Theater, a Houston gem we’ll definitely miss once we’re gone.
Dept. of Iconic GenX Motorcycles, Minneapolis Edition
I found myself wondering what bike Prince rode in Purple Rain, and because it’s 2025 and the Internet exists, it’s easy to find out. The answer was kinda surprising, and kinda not.
What’s not surprising: It was Japanese. In 1985, Harley wasn’t really something most people would’ve noticed or wanted. The investor group led by Willie Davidson had only closed on the purchase from AMF a few years prior, so their recovery was really still a work in progress. The idea of Harley being “back” didn’t really come up until ’90. So: Japan still pretty much owned motorcycling in the US at that time.
What is surprising: What the actual bike was. In the film it’s a bike with a pretty big purple fairing, which gives it the IMPRESSION of being a large machine. Except we all NOW understand that Prince Rogers Nelson was a tiny, tiny man — about 5′ 2″.
Now, in 1984 we didn’t know this. I mean, he obviously wasn’t six foot four or whatever, but exactly how far to the left of the bell curve he fell was definitely not widely understood until much later.
Crucial to maintaining the illusion that one could not steal Prince by stuffing him into a moderate sized dufflebag was avoiding situations where it would be obvious the dude was crazy short, so clearly the producers were not going to put him on, say, a giant Kawasaki like the guys from CHIPS were riding. Having our hero and romantic lead not be able to flat-foot his moto would’ve been a really dumb idea.
So turns out: it’s a heavily customized but very small 1981 Honda CM400A. The big purple fairing was likely made by Honda customization shop Vetter, who were responsible for the original Gold Wing fairings (which were initially only an aftermarket product).
As the name suggests, it’s a 400cc bike. The parallel twin engine made about 27hp, and Honda insists it was technically capable of 85MPH. Even with a tiny, iconic musician driving, that seems optimistic. OTOH, it was 1985, and the 55MPH limit was still the law nationwide. I know from experience that 20HP will handle a double-nickel without complaint, and in the movie Prince uses the bike around town, not for a road trip to Sturgis. “The Kid” in the film is also not rich; a bike like this would’ve been easy to afford, and got excellent mileage to boot.
MORE interesting, though, is that it was equipped with a Hondamatic transmission, not a traditional motorcycle transmission. The rider didn’t have to clutch to shift at all, which is weird as hell. Predictably, the Hondamatic didn’t last long — they were gone by ’83. Interestingly, though, many modern Honda models are available with a true automatic transmission called the DCT. These bikes don’t even HAVE a clutch lever, which is important because it makes it easier for the rest of us to make fun of them. :)
Flags, rags, ferryboats, scimitars & scarves
Fiona Apple has the Whole of the Moon. This may be the finest cover ever. Unseen on the clip, but present on the recording, are Matt Chamberlain, Wendy Malvoin, and Phoebe Bridgers.
A small good thing…
Here is Neko Case covering Iron Maiden some years ago at a live show in Minnesota.
A pedal steel is involved, but it in no way reduces its ferocity. Enjoy.
In case you needed reminding how morally bankrupt the Catholic church is…
According to former board chair Bert Wilson, the food bank’s legal and financial agreements prohibit the use of funds for anything outside its mission of feeding the hungry.
“We have stressed the indisputable fact that our agreements with grant-giving organizations and other partners prohibit any expenditures that are non-secular or do not directly align with our sole mission of feeding the hungry,” Wilson said in a statement on Thursday, calling the decision “shocking and short-sighted.”
The organization cited its contract with Feeding America, which strictly limits how funds can be spent.
Wilson says failing to uphold such guidelines could shutter Second Harvest’s operations, leaving more than 400,000 south Louisiana residents at risk of food insecurity.
Predictably, the Archdiocese has released a statement denying this context, but nobody with a clerical collar and answerable to Rome has any credibility with me. Second Harvest responded to the message thusly:
The Archdiocese video statement, released earlier today and its message to donors of late last week, are remarkable for both they convey says and what they don’t.
Regarding the so-called tolling agreement, Archdiocese representatives were fully aware that Second Harvest was reviewing the proposed agreement and that it was only awaiting full executive committee approval. In direct contradiction to the Archbishop’s unfortunate comment is the fact that an existing agreement covering all parties was already in place until May 1, 2025. Clearly, there was no need for a headlong rush to execute a new agreement. That the Archdiocese jumped the gun by terminating three longtime board members and the non-profit’s CEO speaks volumes regarding their motivations.
More tellingly is the church’s cynical pronouncement of late last week that no Second Harvest donations have “been used for the bankruptcy”. That statement is only true because of the resolve of the now terminated CEO and three board members who were steadfast in their opposition to paying for abuse claims that were none of Second Harvest’s doing.
What’s missing of course, from the Archdiocese statements is any commitment to not ever use Second Harvest funds to help settle bankruptcy claims. Concerned donors and others would be well advised to contact the Archdiocese, their local church Deacons, priests and lay leaders to confirm the church’s real intentions in this regard. Getting such an assurance would go a long way toward resolving this unfortunate dispute and healing the many wounds the Archdiocese actions have caused.
All in All.
It’s easy to feel like everything is terrible right now, but some things aren’t.
This isn’t. This is the 3 surviving members of Nirvana — Grohl, Novoselic, and Smear — reuniting for Fire Aid LA last night, with a rotating slate of vocalists. St Vincent joins them for “Breed;” early Nirvana patron and music god Kim Gordon steps in for “School.” Icon Joan Jett has the mic for “Territorial Pissings.”
And Dave’s daughter Violet sings on “All Apologies,” backed by her father (and also during which Gordon is back on stage on bass, as Novoselic shifted to accordion).
A fun thing to note here is that when famously-giant Novoselic (listed online at slightly over 2m, or about 6′ 7″) kneels in tribute to Jett at the end of her song, he’s still nearly as tall as she is. (And she’s not especially short, apparently; the Internet says 5’5″.)
Moonrise Kingdom, again
My love for Anderson’s 2012 film Moonrise Kingdom is very well documented. Somehow, though, I missed that, in the run-up to the release of Asteroid City, there had been some additional “Andersonia” floating around.
Included was this short interview with Jared Gilman and Kara Wayward, who played Moonrise’s romantic leads. The catch is that now they’re adults. The whole thing is very charming and delightful. Enjoy.
What makes you happy?
Reviewing an old thread on Facebook, wherein I was being grouchy about something, I find that someone asked “what makes you happy?” by way of contrast.
I replied with this, slightly edited. These are dark days. Don’t forget there is still joy in the world.
Erin. Bacon. Our cats. My nieces and nephew. My brother. Cool tech. Beautiful music. That feeling of being safe and warm at home with your people and pets when it’s cold and wet outside. Getting stronger on my bike. Our impending vacation. Erin’s ongoing experiments with the new slow cooker. My friends, and their beautiful children, even the ones we don’t see all that often. Houston in general. Houston’s arts community in particular. Mechanical watches. Fountain pens. Good wine. Great whiskey. Hubcap burgers. Alabama football, most of the time. The fact that more people can get health insurance today than a year ago. The migas at Guadalupana. Sherlock and Doctor Who. The impending release of the new Robert Ellis record. The fact that we have a great record store in Houston. My Kindle. Macintoshes. The prospect for a good year, businesswise. Photography.
Dept. of reaping what was sown
According to a well-sourced (US Bureau of Labor Statistics) post on Reddit, Texas has lost about 50% of its OBGYN practitioners since 2019; in that same time period, the number of OBs in California (similar in size and GDP) has increased dramatically.
50 years is a long time
You should make time — it’s only about 7 minutes — for this really great tribute edit of SNL musical guests, released as a trailer for Questlove’s 3-hour documentary on the history of music on SNL. It drops tonight; I can’t wait.
In the world I grew up in, live musical performances on TV were more common and mainstream. Now, it feels like SNL is one of the last places where that tradition continues.
Seen Here…
SNL’s Weekend Update has been running a GREAT gag for a while in pieces about Mitch McConnell wherein they show a photo and say “seen here…”
Dept. of Lost Causes
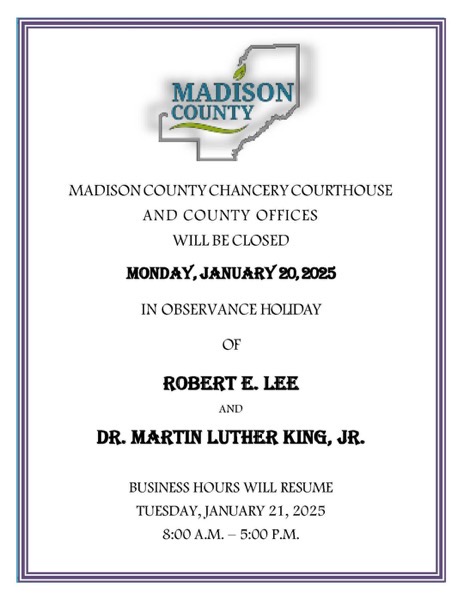
Comes now this alert, via my sister, about the upcoming holiday in our home state:
Sometimes, when it comes out in conversation that I’m from Mississippi, people ask what that was like.
This is a great example. The whole state is STILL mired in Lost Cause bullshit to the point that ROBERT E. LEE’S BIRTHDAY is celebrated ALONG SIDE Martin Luther King’s. Over there, committing treason in defense of slavery is apparently just as laudable as fighting for civil rights. This combination is not accidental — like most of the Civil War monuments, it came later, as a thumb in the eye of those who’d seek to diminish the myth of the Lost Cause. Coerced by the rest of the country to enshrine Rev King’s birthday as a holiday, they chose to combine it with Lee’s.
What assholes.
I’ve said this before, but I’ll say it again: in high school, we were taught — and had to parrot it back, on tests — that the Civil War was more about states’ rights than anything else, and that slavery was a footnote. This was only a viable pedagogical position because the curriculum went out of its way to NEVER EVEN MENTION that the seceding states literally wrote and circulated documents detailing in no uncertain terms why they were prepared to go to war over leaving the union.
Had those documents been mentioned AT ALL, teaching this states-rights lie would’ve been utterly impossible. Mississippi’s document for example, starts like this:
In the momentous step which our State has taken of dissolving its connection with the government of which we so long formed a part, it is but just that we should declare the prominent reasons which have induced our course.
Our position is thoroughly identified with the institution of slavery– the greatest material interest of the world. Its labor supplies the product which constitutes by far the largest and most important portions of commerce of the earth. These products are peculiar to the climate verging on the tropical regions, and by an imperious law of nature, none but the black race can bear exposure to the tropical sun. These products have become necessities of the world, and a blow at slavery is a blow at commerce and civilization. That blow has been long aimed at the institution, and was at the point of reaching its consummation. There was no choice left us but submission to the mandates of abolition, or a dissolution of the Union, whose principles had been subverted to work out our ruin.
Disingenuous people ask silly questions like “what even IS institutional racism?” This right here is a great fucking example: going out of your way to limit exposure to the historical record in order to suppor the teaching of an outright lie.
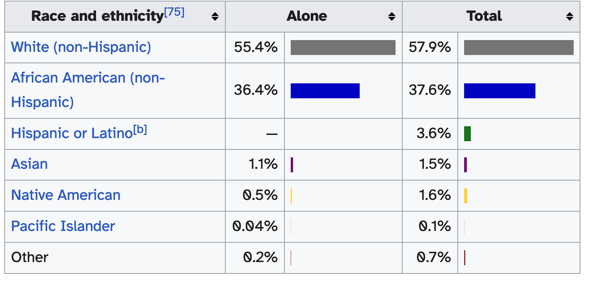
Obviously, everyone there isn’t terrible, but it’s safe to say the majority of (white) population mostly doesn’t mind this sort of thing. Why do I paint with such a broad brush? Well, it’s numbers.
See, it’s absolutely true that (for example) about 38% of voters there voted for Harris in November. That’s not nothing, right? I mean, as states go that’s a big margin, but it’s still a lot of votes.
However, if we go look at the demographics of the state, we see a very similar split; make of this what you will.
There’s a final note I’ll make. Mississippi is reaping what it’s sown. People with options don’t choose to live there. It’s a smaller state now, relative to the rest of the country, than it was when I was growing up. I was surprised, a little, to discover it’s down to 4 House seats now; in my youth there, it had 5. More shocking is the fact that, at one point in the earlier 20th century, it had 8.
You can measure that another way, too. When I was in high school, I was one of 8 National Merit scholars; a 9th young man qualified for the National Achievement program, so let’s work with that as a number. Of those folks, only one chose to make his life there. 1, out of 9.
Because we had options.
(Not for nothing, but it’s both tragic and heartwarming that today I saw a message from one of the others on Facebook announcing he’d lost his house in the Palisades fire, which was almost immediately replied by by another of our group who lives on the other side of the country. Nerdy kids stay friends, yo.)
Insurance companies are evil.
Go read this story, and in particular pay attention to this paragraph, which talks about a hypothetical attempt to pay out of pocket for care denied by the insurer:
But we soon learned another sinister result of hyper-privatization of health insurance—even if we had the excessive means to pay the hundreds of thousands of dollars out of pocket, the hospital would not accept the funds. Why? The industry is such that not only do insurance companies deny 51% of claims, they have enacted policies forbidding people from paying for the critical medication they need out of pocket, lest the insurance company lose control and revenue. “Either you pay us, or you pay no one,” is a line you’d expect out of a mafia handbook—not out of a health provider. This is not health insurance, this is health exploitation.
Single payer now.
Well, this is interesting
As of Saturday, I am now 20,000 days old.
Nick Cave confronted the milestone with a film, but I reckon I’ll be content with this post.
It turns out, “sucks” is relative
I’m not an NFL fan, but it has not escaped my notice that Detroit is doing well this year. This seems odd to me, as an NFL outsider, because my definite impression is that the Lions have traditionally been helpless.
So I went looking, and found this excellent Wikipedia page, which includes a sortable table of all NFL teams by regular season record.
The table, interestingly, includes a column for games played. There’s a HUGE range here. The OG teams like Chicago, Green Bay, etc, are all over 1400 games at this point — but the newest team, our hometown Houston Texans, are at only 355.
Anyway, a few interesting takeaways:
First, the actual RANGE of regular season records is narrower than you might think. The winningest team is, despite my understanding of contemporary performance, Dallas. They’re at .576. The worst is Tampa, at .406.
Detroit IS towards the bottom; they’re 26th out of 32 at .455. But that’s pretty close to even, right?
The bottom five are, in descending order, Atlanta (.439), Houston, Jacksonville, Arizona (nee St Louis, and with Chicago the only remaining OG team), and Tampa Bay.
The “worst” team over .500 is the Rams, at .506, in 16th place.
Playoff records are also available. To probably no one’s surprise, given the Brady years, New England is that the top of that list. They’re at .627 in the postseason, followed by San Francisco (.613), Green Bay (.586), Baltimore (.567), and the Steelers (.563).
At the bottom, we find Cleveland at .353.
This sent me down a rabbit hole, because I thought I remembered that “Cleveland” of today is actually an expansion team, and that the “real” Browns moved to Baltimore to become the Ravens.
This was functionally true at the time (1995), but when Art Modell moved the squad to Baltimore he took the players, personnel, etc., the NFL treated Baltimore as an expansion team and left the Cleveland IP in trust and suspended. The NFL guaranteed that Cleveland would get a new Browns no later than 1999. Sure enough, when Cleveland resumed play in ’99, it was with an expansion draft, but this expansion team got to “inherit” the stats and history of the Browns. So at Wikipedia, Cleveland is credited with a 1950 founding date and 1,053 games played, while Baltimore is treated as a team founded in 1996. This is some serious doublethink bullshit, candidly, but it’s football so whatever.
Search is SO BROKEN
I just heard about the underground fire in Williamsburg, WV, which of course reminded me the OTHER great underground American fire in Centralia, PA — which has been burning since 1962.
Anyway, I searched for “Centralia PA” at DuckDuckGo, and the top links returned were ad links for Expedia, Hotels.com, and Tripadvisor, all promising me deals on 5-star hotels in Centralia.
Um.
HEY LOOK! MUSIC!
FIRST:
Ol’ Man Dorman sent me this clip of a Paul McCartney show in CDMX a couple days ago wherein Jack White and St Vincent join him and his band for the conclusion of THE END. It is delightful.
THEN:
TV on the Radio resurfaced for an absolutely barn-burner of a performance on Jimmy Fallon, heralding both a criminally short tour AND the 20th anniversary reissue of their debut album, which I’m trying to decide if I’m gonna go buy RIGHT THE FUCK NOW.
Happy birthday to me?
Two days ago this humble site had its 24th birthday; my first entry here was on the 20th of November in the Year of Our Lord Two Thousand.
I had but 20 posts that year. I didn’t get super verbose until 2003, and if I’m honest it’s probably the creeping horror of the Bush administration that did it. You can look over to the right, under the Archives header, and see the productivity curve. Peak was 2007, with 1,147 posts.
There have been 28 this year. Only 44 last year. I haven’t hit 100 since 2016. Habits die, I reckon.
I do regret every long form post or reply I wrote for Facebook or Reddit or Metafilter now, which ought to be instructive. There’s no good reason to write and post anywhere that you don’t own.
Anyway, Heathen limps along. I have no plans to stop.
New Frontiers in Ridiculousness
So, Triumph has a giant-ass bike called the Rocket 3. It’s an inline 3-cylinder engine with 2,458cc displacement. That’s legit a car-sized engine. Motorcycles are almost exclusively under 1,000 CC — you may recall people talking about having a “500” or a “750” in years past; those were displacement numbers in CCs (and, honestly, those were ENTIRELY ENOUGH in a world where the national speed limit was 55).
Today, top-end sport bikes — bikes capable of 200+ MPH — have 1,000 cc engines. These so-called “liter bikes” are rightly viewed as widowmakers because, well, if you get too happy with the throttle you’re gonna have a real, real bad day (and so are the people around you).
The big cruiser makers (e.g. Harley) have traditionally stuck with very traditional engine types, and so they were pretty much the only folks out there still using (and requiring) displacement to get power. The top-end Harley touring bikes are well over a liter in displacement, though obviously they mark their engines in cubic inches on account of Freedom. Even so, I think the biggest one available is still only about 1,800 cc. The power per unit of displacement with Harley is, though, notoriously poor. (Tradition!)
Anyway, the Rocket 3 exists. That almost 2.5L engine gives the bike 180 horsepower, and it comes with a similar torque figure. That’s CRAZYTOWN. Most leaned-over fairing-clad sport bikes don’t make that much power, and this is a bike with an upright riding position and zero wind protection. I mean, sure, it’s a big bike — 40% heavier than mine — but it’s nothing like the nearly half-ton tourers you see on the roads that it’ll compete with.
Of course, such absurdity comes at a cost: the base model Rocket 3 is about $25,000, which is HUGE money for a motorcycle (my first one cost less than $5k NEW). All this together means the Rocket 3 is what they call a “halo model” — high price, extraordinary levels of charisma, and low sales, like the Viper your local Dodge guy had for a while. A dealer gets a couple to showcase on the floor, but he doesn’t expect to sell many.
But Wait There’s More!
In my email this morning — I’m on the Triumph list — came the announcement of a special edition of the Rocket 3 in honor of that paragon of motorsports safety, Evel Knievel.
Gaze in wonder at this $30K variant of an already very, very silly motorcycle.
“All of that explains how an octogenarian rancher named Arthur Schubarth yesterday found himself sentenced to six months in federal prison for cloning a sheep.”
Well, this is a tale.
It’s as though empathy and caring about other people are completely alien to them
In Ohio, we have a much-watched Senate race between incumbent Democrat Sherrod Brown and right-wing pro-lifer Bernie Moreno. As TPM notes, this could’ve been much more of an “abortion race” had Ohio progressives pushed to have their pro-choice referendum on the ballot this year instead of last year (it passed).
Moreno, for his part, should have been over the moon to avoid having this be a referendum on abortion (given that literally NO polling shows the GOP position as popular post-Roe), but you wouldn’t know it from his comments:
“You know, the left has a lot of single issue voters,” Moreno said. “Sadly, by the way, there’s a lot of suburban women, a lot of suburban women that are like, ‘Listen, abortion is it. If I can’t have an abortion in this country whenever I want, I will vote for anybody else.’ … Okay. It’s a little crazy by the way, but — especially for women that are like past 50 — I’m thinking to myself, ‘I don’t think that’s an issue for you.’”
Yes, it’s entirely bananas that these women would care what happens to OTHER women, right? The Republican position on so many issues boils down to “I got mine, fuck you,” and that POV absolutely ignores the very possibility that one human might care what happens to other people.
Today in Great Headlines
Dept. of Pop Culture Artifacts
I see in the news that Tito Jackson, 3rd eldest of the Jackson Family and former member of the Jackson 5, has passed away. He was not quite 71.
I think of the Jackson 5 as a long-ago thing, but of course they weren’t, and also of course they were all terribly young in their heyday — they started in 1964; my personal favorite tracks came in 1969-1970 — so I looked it up.
Joe and Katherine Jackson had 10 kids between 1950 and 1966, including a set of twins where only one survived. Jackson 5 members in bold.
- Rebbie Jackson, 1950, is now 74.
- Jackie Jackson, 1951, is now 73.
- Tito Jackson, 1953-2024, was not quite 71.
- Jermaine Jackson, 1954, turns 70 in December.
- La Toya Jackson, 1956, is now 68.
- Marlon Jackson, 1957, is now 67.
- Brandon Jackson, 1957-1957.
- Michael Jackson, 1958-2009, was 50 when he died. Had he lived, he’d have turned 66 last month.
- Randy Jackson, 1961, turns 63 in October. He replaced Jackie in the Jackson 5 in 1975.
- Janet Jackson, 1966, is 58.
And now: Teaching a Komodo Dragon about Supertramp
See, they used to be called Daddy, and were way more of a prog-rock kind of bent — GODDAMMIT LOOK AT ME WHEN I’M TALKING, YOU PREHISTORIC FREAK — until probably around 1973 or so, when they added Bob Siebenberg, among other new members — STOP EATING THE FURNITURE, YOU FUCK — and got signed. In 1974, they had their first hit, which turned out to be one of many — JESUS FUCK YOU STINK, YOU KNOW THAT? — that included 1975’s “Dreamer” and the also-solid B-side “Bloody Well Right.” DO NOT FUCKING BITE THE INTERN! CHRIST! The late 1970s brought their huge hit, “Breakfast in America,” that included the songs anyone who grew up in the 1970s — I’M STARTING TO THINK YOU DON’T REALLY GIVE A SHIT ABOUT SUPERTRAMP, YOU GENETIC THROWBACK — knows by heart, including “The Logical Song,” “Goodbye Stranger,” and “Take the Long Way Home.”
You know what? Fuck this. You and your poison spit can go listen to One Direction for all I care. I’m out.
So, who’s qualified?
I fell down a rabbit hole of Wikipedia research here based on my irritation at the “Harris isn’t qualified” babble from the right.
So, first and self-evidently, she’s qualified. She’s been VP, she’s been a Senator, and she held elected office at the state and local level before that. This is a solid resume, and turns out to be a pretty common path. But! Let’s look at data.
First, let’s talk about VPs
I looked back 100 years, to Coolidge, which means 17 presidents. In that time, 7 former VPs have held the Oval Office:
- Calvin Coolidge assumed office after Harding, and was elected on his own;
- Harry Truman assumed office after FDR, and was elected on his own;
- Lyndon Johnson assumed office after JFK, and was elected on his own;
- Richard Nixon was Eisenhower’s VP (1953-1961) before being elected on his own in 1968;
- Gerald Ford assumed office after Nixon resigned, but did not run on his own;
- George H. W. Bush was Reagan’s VP and was elected after Reagan’s 2nd term; and
- Joe Biden was Obama’s VP (2009-2017) before being elected on his own in 2020.
This is an interesting set.
VPs who ascend to the Presidency are the majority here, even though it hasn’t happened since 1974: that’s 4 of the 7. Three of those sought their own terms, and won them.
Ford, famously, did not run — and in fact never ran at all, which is wild. He ended up President without a single electoral vote EVER since he was appointed to replace Agnew, and then Nixon resigned. It’s a turn of events worthy of fiction, and in fact I’m pretty sure that “appointed VP and unexpectedly promoted” is how Tom Clancy’s Jack Ryan ends up in the White House.
Anyway, one take-away is that assuming office DOES give you a leg up, electorally speaking, since everyone who did so and sought the office on their own won a term.
The other interesting thing is that I would have assume that non-promoted VPs really only have a good shot at election if they run immediately after their president’s term ends, but that’s wrong (well, n=3, so …).
Of the 3 non-promoted VP presidents, only one was elected immediately after his VP term ended (G.H.W. Bush). The other two sat out: Nixon left office in 1961 and didn’t become president until 1969. Biden, of course, sat out the 2016 cycle before running and winning in 2020.
And so: Qualifications
Let’s take as read that the corpus of former presidents gives us a good metric for “what should be on a presidential hopeful’s CV?”
“Was a VP” is the most common former qualification of the last 100 years of presidents (7 of 17, so about 41%).
“Was a Senator” and “Was a Governor” are tied at 6 each (35%).
Former Senators (also a VP indicated by italics)
- Truman
- Kennedy
- Johnson
- Nixon
- Obama
- Biden
Former Governors:
- Coolidge
- Roosevelt
- Carter
- Reagan
- G. W. Bush
- Clinton
If we look at the overall picture of electoral / leadership history, there’s really not that many categories of prior jobs to look at, so it seems reasonable to assign point values and rank ’em.
- Being VP gets you 5 points.
- Being a Governor gets you 4
- Being a Senator gets you 3
- Being a House rep gets you 2
- Any other elected office (local or state level) is worth 1
- Any other significant appointed position (Cabinet posts, ambassadorships, etc) is worth 0.5
That’s an off the cuff ranking, but it’s worth throwing at the wall, right?
Top dog is Coolidge with 13 points. He was VP (5), Governor (4), held 3 state offices (LtGov, Mass. Senate, Mass. House) and 1 local one (Mayor). (Of course, he’s also not considered a very good president, but at least his resume was solid.)
Then we have a 3-way tie at 10:
- Johnson (VP, Senator, Rep);
- Nixon (VP, Senator, Rep); and
- HARRIS (VP, Senator, 2x additional offices)
So, uh, tl;dr?
MAGAts should STFU about her resume. Especially given that the bottom of this list, with zero points, is Orange Jesus. He’s also the only one to score ZERO. We’ve had other presidents with no prior electoral experience, but they typically held executive-level appointments (Hoover, 2, scoring 1 point) or several big-ticket military billets (Eisenhower, who had 3, scoring 1.5).
Life imitating Comedy?
So, this morning, I saw on Ars Technica this really strange story:
Apparently, the Christian Hate Chicken folks are taking a page out of . . . JCPenny’s?
We live in a very strange timeline.
One old, one new
I became an uncle for the first time in January of 2006. For a variety of reasons — mostly, I suspect, because phones weren’t cameras and I didn’t get back into photography until a later — the earliest picture I have of her is this, when she’s about 13 months:

Erin just sent me a new picture of FirstNiece. This is her with her packed car, about to drive away to college:

Time, man. It’ll get you.
Godspeed, Caroline.
Nick Cave on Colbert
Make time for this if you’re a fan at all, or even if you’re not.
I do love a great short comedy
This is GOLD. Wait’ll they hear about Arlington.
Dept. of Records
It’s been a pretty good Tour so far this year, with two records of note.
The first came a few days ago, when Eritrean rider Biniam Girmay became the first Black rider to win a stage. The reaction in his team car is pretty great.
Then, today veteran rider Sir Mark Cavendish won the 5th stage of the 2024 Tour de France. Aptly, the Manx Missile won in a sprint, 16 years after he won his first stage.
Until today, the record for Most Stage Wins in the Tour was held by cycling god Eddy Merckx, a Belgium rider who dominated the sport in the 60s and 70s. He won the Tour 5 times outright, and bagged the points prize 3 times and the mountains award twice, all on his way to winning a stunning 34 stages, a record he set 49 years ago. (I could go on and on here, but suffice it to say that Merckx dominated cycling in a way that really exceeds the huge footprint Jordan left on basketball, or that Tiger had on golf. He won everything over and over, in a way that no one has been able to approach since, partly because cycling has become enormously specialized. Cavendish has the stage win title now, for example, but he’s a sprinter and has never been in contention for the overall Tour.
Here’s some video. The speeds are in kilometers, but it’s worth noting that they finished uphill, into the wind, at forty miles an hour.
The table on the TdF records page is pretty wild and VERY stable. Aside from Cav today, you have to read down the list to the current 13th place rider to see a date in the 21st century (Marcel Kittel, who won his 14th in 2017).
The only other currently active rider (aside from Cav) is wonderkind Tadej Pogačar, currently tied for 16th place with 12 wins (including Stage 4 of this year’s race).
That number will go up; Tadej is only 25, and is the odds-on favorite to win in Paris this year. Not for nothing, but he’s the closest thing to an all-around threat we’ve seen since Merckx — he’s won the TdF outright twice, and in both years ALSO won the Mountains classification. He’s also won the Giro, and sits at top spot of the UCI road racing rankings. He’s compared to Eddy so often there’s a whole section of his Wikipedia article about it.
Will he beat Cav? I’m fresh out of crystal balls, but it’s pretty easy to imagine a world where Tadej ends up in the top 5 (which would require 23 wins). He’s only 25, and racing stays viable into one’s 30s. (Cadel Evans won the Tour at 34 back in 2011.) If he stays healthy, and wins at his current pace (so, call it 2.5 or 2.75 stage wins per tour), then Cav’s record won’t last past the mid-2030s.
But that’s a big if.
And that cow’s name? CHRISTOPHER WALKEN.
Half a century ago, an English farmer lost his watch.
Dept. of Unlocked Catalog Memories
My 80s youth was awash with catalog companies. In the absence of the Internet, paper-based distance-shopping was immensely popular! There were tons of these; the most well remembered were firms like The Sharper Image that eventually became a sad mall store, but my old favorite was the DAK catalog — which, somehow, I forgot about entirely until I saw this blog post that’s been sitting in an open tab for six months.
Enjoy!
He gets them from the sheep.
I present the wrongest Christmas carol ever, safely now in June:
Thousands of tiny white things inside of his drum.
teeth #sheep #drum
The Most Important and Earliest Self-Referential Texts
Well, for me, anyway:
The Monster at the End of This Book, obviously, but also and more thrillingly
Duck Amuck, which you probably haven’t seen in far too long. But it’s on YouTube. Enjoy.
I have a strong feeling that the affection GenX obviously has for breaking-the-fourth-wall — e.g., Deadpool on page and filme — has at least some of its roots in these two documents.
Joe Stands Alone
Something interesting came up the other day: in conversation elsewhere, I learned that Joe Biden is the ONLY member of his generational cohort (“The Silent Generation,” born between 1928 and 1945) to ever be President, and given the age of that group it’s likely none will follow him.
After Ike, POTUS was always a member of the so-called “Greatest Generation,” born between 1901 and 1927. They fought the war, hence the name. So, after Ike — a member of the prior “Lost” generation, born in 1890 — we had a parade of Greatests for thirty years:
- JFK, born 1917, took office in 1961, and turned 44 his first year in office
- LBJ, 1908, 1963, 55
- Nixon, 1913, 1969,56
- Ford, 1913, 1974, 61
- Carter, 1924, 1977, 53
- Reagan, 1911, 1981, 70 (which was a huge point of discussion at the time)
- GHWB, 1924, 1989, 65
Then we skipped the Silent folks entirely, and the Boomers took over for nearly another 30 years:
- Clinton, 1946, 1993, 47
- GWB, 1946, 2001, 55
- Obama, 1961, 2009, 47
- Trump, 1945, 2017, 71
It’s only then that a member of the Silent cohort got elected, in what was really a black-swan electoral event in lots of ways — absent the very specific factors of the 2016 race, it’s easy to imagine a world where no Silent gets elected at all. Instead, Joseph R. Biden, born 1942, was inaugurated in 2021, and turned 79 his first year in office.
It seems clear he’ll remain the only Silent to ever sit in the Oval.
That got me thinking: Why?
Turns out? Numbers. The Silent cohort was comparatively small — especially compared to the groups that came before and after. There are lots of reasons for this, but the biggest ones are probably the Depression and the War depressing birth rates.
Pew suggests the Silent group was “only” about 47M births; compare that to the Boomers at 76M.
All this points me to an uncomfortable realization: my own cohort, GenX, is also a small group sandwiched between two much larger generations (the Boomers and the Millennials). That could lead to the Oval skipping us, too. :(
Oh well.
Books of 2024, #6: Babel by R. F. Kuang
You’d think I’d get tired of hating books the SF critics love, but here we are again.
Babel is a mess. It’s yet another coming-of-age tale in SF, which is something I’m getting really tired of across the board; I mean, is it impossible for authors to imagine something interesting happening to adults? Fine. Whatever. If that was the only thing I disliked, this would be a different post.
The basic argument is that our point of view character (Robin) is a half-Cantonese youth orphaned by a cholera outbreak. Predictably, he’s “rescued” from poverty by an English academic, who adopts him as his “ward” and takes him back to Oxford to join the fictional Translation Institute there.
In the world of Babel, a sort of magic exists based on the user of silver bars engraved with matched-pairs of words in translation. The effect is derived from the tensions and implications inherent in translation. This is clever, but not NEARLY so clever as Kuang clearly thinks it is; one serious shortcoming of the book is an ENDLESS PARADE of footnotes describing this-or-that matched pair. Often, the footnotes are in untranslated Chinese, because I guess why not?
But even this bit of babble isn’t the main problem with the book. Publisher’s Weekly says it better:
Publishers Weekly negatively reviewed the novel, saying, “Kuang underwhelms with a didactic, unsubtle take on dark academia and imperialism.” They explained, the “narrative is frequently interrupted by lectures on why imperialism is bad, not trusting the reader or the plot itself enough to know that this message will be clear from the events as they unfold. Kuang assumes an audience that disagrees with her, and the result keeps readers who are already aware of the evils of racism and empire at arm’s length. The characters, meanwhile, often feel dubiously motivated.”
This is something I’ve joked about before as “Rand’s Disease.” Like lots of bright kids, I read Atlas Shrugged in high school. Ayn Rand’s books are notionally novels, but they’re not REALLY. What they are are long tirades about her philosophy masquerading as fiction. The characters are wooden and poorly fleshed out. Motivations are questionable. Reactions are bizarre. This is what happens when your priority is something other than the novel itself.
Kuang falls prey to this at every turn. Her characters are wooden and shallow. Motivations are sketchy at best. They all feel like sock puppets in a pantomime about the evils of colonialism. I’d say “cut out the endless rants and you’d have something,” except absent the pages and pages of anticolonialism I’m not sure what would be left.
And yet: it won the Nebula. I think SF people just must not care very much about the actual craft of fiction, and consider Big Idea shit to be the higher value, because holy hell this is a problem I run into a LOT when I read an “award-winning” SF text. In Babel’s Nebula year, it beat out the drastically better crafted Nona the Ninth, for example. Reading backward in the list of Nebula winners, I see only 7 genuinely excellent novels in the winner slots since 2020 (Butler’s Parable of the Talents; Gaiman’s American Gods; Chabon’s Yiddish Policemen’s Unions; Bacigalupi’s The Windup Girl; Leckie’s Ancillary Justice; Jemisin’s The Stone Sky; Wells’ Network Effect).
Others obviously disagree, but I think my takeaway is that the Nebula isn’t a good indicator for quality for ME. (The Hugo list is marginally better, but there’s other issues there.)
What we talk about when we talk about the Stones
So geriatric oldies act “The Rolling Stones” played here on Sunday. I’ve seen them before, most recently 30 years ago, and candidly it was already a bit hard to swallow 50+ Mick preening about when Clinton was president. At 80, it’s damn near a novelty act — and a gradually sadder and sadder one, given that at this point only Mick and Keith remain of the band that gave us the string of groundbreaking records in the late 60s and early 70s. Wyman has been retired since 1993. Charlie Watts has been dead for two years, which is hard to fathom.
Sure, they have Ron Wood as the “new guy” with half a century behind him, and that’s not NOTHING, but he’s also not on the good material. He joined because Mick Taylor had left, and his exit crippled the band creatively — at least, compared to what they accomplished with him. Taylor was in the band from Let It Bleed (1969) through I’s Only Rock And Roll (1974); that era includes Sticky Fingers and Exile on Main St. The Stones songs you know are overwhelmingly from 1974 or earlier, with some exceptions, and a GREAT chunk of their best material happened with Taylor on 2nd guitar.
In keeping with that, of the 18 songs they played Sunday, 11 were from 1974 or earlier. The newer tracks include 2 each from 1978’s Some Girls (“Beast of Burden” and “Miss You”) and 1981’s Tattoo You (concert favorite “Start Me Up” — realistically speaking, their only true hit since 1974 — and “Little T&A”).
The Tattoo You tracks are, at this point, 43 years old; they were also the youngest songs played aside from the obligatory sampling of last year’s Hackney Diamonds. Even with the new tracks in the mix, the average song age Sunday is old enough to schedule a colonoscopy. If you drop the 3 youngsters as outliers, the average age shoots up to 53.
Anyway, he’s a review — and setlist — from the other night, written by my pal Andrew. He’s awesome. It’s a fun read, even allowing for my snark about these octogenarians and their nostalgia tour.
Here’s something worth noting
(This whole post h/t to Dorman.)
Louis Gossett, Jr., died today, at the age of 87.
Something interesting about Mr Gossett is that when he won his Oscar for Supporting Actor for An Officer and a Gentleman, he was only the third African-American person to win an acting Oscar of any kind. (Edit: a previous version of this post incorrectly stated he was only the 3rd Black winner of any Oscar at all, and that’s not true; Isaac Hayes won Best Song in 1973.)
Most famously, Hattie MacDaniel won for Supporting Actress in 1939 for Gone With the Wind. A Black person would get a statue again until Sidney Poitier won Actor for Lilies of the Field in 1963 (which was his second nomination in the category; he’d been there in 1958 for The Defiant Ones.
And the next Oscar after that was 19 years later and Mr Gossett.
There’s a lot at the aforementioned link, but your timeline of Actor category wins is:
| No. | Year | Category | Actor | Film |
|---|---|---|---|---|
| 1 | 1939 | Supporting Actress | Hattie McDaniel | Gone with the Wind |
| 2 | 1963 | Actor | Sidney Poitier | Lilies of the Field |
| 3 | 1982 | Supporting Actor | Louis Gossett, Jr. | An Officer and a Gentleman |
| 4 | 1989 | Supporting Actor | Denzel Washington | Glory |
| 5 | 1990 | Supporting Actress | Whoopie Goldberg | Ghost |
| 6 | 1996 | Supporting Actor | Cuba Gooding, Jr. | Jerry Maguire |
| 7 | 2001 | Actor | Denzel Washington | Training Day |
| 8 | 2001 | Actress | Halle Berry | Monster’s Ball |
| 9 | 2004 | Supporting Actor | Morgan Freeman | Million Dollar Baby |
| 10 | 2004 | Actor | Jamie Fox | Ray |
| 11 | 2006 | Supporting Actress | Jennifer Hudson | Dreamgirls |
| 12 | 2006 | Actor | Forest Whitaker | The Last King of Scotland |
| 13 | 2009 | Supporting Actress | Mo’Nique | Precious |
| 14 | 2011 | Supporting Actress | Octavia Spenser | The Help |
| 15 | 2013 | Supporting Actress | Lupita Nyong’o | 12 Years a Slave |
| 16 | 2016 | Supporting Actress | Viola Davis | Fences |
| 17 | 2016 | Supporting Actor | Mahershala Ali | Moonlight |
| 18 | 2018 | Supporting Actress | Regina King | If Beale Street Could Talk |
| 19 | 2018 | Supporting Actor | Mahershala Ali | Green Book |
| 20 | 2020 | Supporting Actor | Daniel Kaluuya | Judas & The Black Messiah |
| 21 | 2021 | Supporting Actress | Ariana DeBose | West Side Story |
| 22 | 2021 | Actor | Will Smith | King Richard |
| 23 | 2023 | Supporting Actress | Da’Vine Joy Randolph | The Holdovers |
I don’t watch every year, but I absolutely remember 2001 with crystal clarity. Denzel and Halle, on stage together, was electric.
Additionally, in terms of the biggie awards, Steve McQueen won Picture for 12 Years a Slave. No African American has ever won Director despite nominations by John Singleton (Boyz n the Hood), Lee Daniels (Precious), Steve McQueen (12 Years a Slave), Barry Jenkins (Moonlight), Jordan Peele (Get Out), and Spike Lee (BlacKKKlansman).
Voyager is dying.
In 1977, we humans did something audacious. We launched Voyager 1 towards the outer planets, with an idea that maybe we’d get more. It was the second craft, after its sibling Voyager 2, to fly past Jupiter, and was the first to take close-up photos of Jupiter’s moons when it arrived there some 18 months later. By 1980 Saturn was in its sights, where it gave us the first images of Titan and Tethys.
By the end of 1980, it entered what NASA referred to as its “extended mission,” flying ever father from Earth. In 1990, just before its camera shut down forever, its operators pivoted it to take the famous Pale Blue Dot photograph, about which Carl Sagan said:
That’s here. That’s home. That’s us. On it everyone you love, everyone you know, everyone you ever heard of, every human being who ever was, lived out their lives. The aggregate of our joy and suffering, thousands of confident religions, ideologies, and economic doctrines, every hunter and forager, every hero and coward, every creator and destroyer of civilization, every king and peasant, every young couple in love, every mother and father, hopeful child, inventor and explorer, every teacher of morals, every corrupt politician, every “superstar,” every “supreme leader,” every saint and sinner in the history of our species lived there – on a mote of dust suspended in a sunbeam.
Voyager was built in the 1970s, with the technology available in those years. Over time, the radioactive isotopes it uses for energy have decayed, as they are wont to do, and with that decay came a gradual loss of power. Systems had to be shut down, one after the other, including the aforementioned camera (though one wonders how much of a loss that was; where it is, there is nothing to see).
It left the Solar System 14 years ago, and kept going. They thought we might get a solid 3 years out of it, and yet here we are, four decades later, talking about it.
Voyager 1 is the farthest spacecraft from Earth, and the margin is not close. It is some 15 billion kilometers away now. Radio signals from Earth take some 22 hours to reach it. The reply takes, of course, another 22. That record is unlikely to be broken; as noted here, there are only two others in the race: Voyager 2 and New Horizons, and due to mission parameters both will likely die well before they exceed Voyager’s distance.
Voyager, though, is dying. In December the data stream back from it — data that spent 22 hours in transit — became gibberish. Nobody knows why; it could be a thousand thousand things, but there is no way to fix it. CrookedTimber continues:
Voyager Mission Control used to be a couple of big rooms full of busy people, computers, giant screens. Now it’s a single room in a small office building in the San Gabriel Valley, in between a dog training school and a McDonalds. The Mission Control team is a handful of people, none of them young, several well past retirement age.
And they’re trying to fix the problem. But right now, it doesn’t look good. You can’t just download a new OS from 15 billion kilometers away. They would have to figure out the problem, figure out if a workaround is possible, and then apply it… all with a round-trip time of 45 hours for every communication with a probe that is flying away from us at a million miles a day. They’re trying, but nobody likes their odds.
So at some point — not tomorrow, not next week, but at some point in the next few months — they’ll probably have to admit defeat. And then they’ll declare Voyager 1 officially over, dead and done, the end of a long song.
(See also: It’s Quieter in the Twilight, and excellent documentary from last year about the folks still working on Voyager.)
Of course, even dead Voyager will continue moving, forever, unless it hits something. It’s not pointed towards any star we know, but that could change in a long enough time scale. After billions of years (yes!), our Milky Way galaxy will collide with its neighbor, Andromeda. From this article:
After those 5 billion years, modeling is tricky. That’s when the Milky Way is due to collide with its massive neighbor, the Andromeda galaxy, and things get messy. “The orderly spiral shape will be severely warped, and possibly destroyed entirely,” Oberg said. The Voyagers will be caught up in the merger, with the details difficult to predict so far in advance.
Meanwhile, the vicarious sightseeing continues. Oberg and his colleague calculated that in this 5-billion-year model-friendly period, each of the Voyagers likely visits a star besides our sun within about 150 times the distance between Earth and the sun, or three times the distance between the sun and Pluto at the dwarf planet’s most distant point.
Precisely which star that might be, however, is tricky — it may not even be a star we know today.
“While neither Voyager is likely to get particularly close to any star before the galaxies collide, the craft are likely to at least pass through the outskirts of some [star] system,” Oberg said. “The very strange part is that that actually might be a system that does not yet exist, of a star that has yet to be born.”
Two Star! A forgotten 1990s Fox sitcom…

This is the photo they used for the criminally short-lived Two Star sitcom Fox put together in the early 1990s. They fucked up the scheduling FOUR DISTINCT TIMES, each time putting it opposite absolute juggernauts from the legacy networks (e.g., at one point, CHEERS), and so only 6 episodes aired. More’s the pity, Fox has refused to release it on home video or streaming, so even those six are really only available on grainy dubs from VHS. There are RUMORS of a Halloween special, but even 30 years later no footage has leaked.
KNOWN EPISODES (fall, 1992)
1.01 PILOT: A trio of string musicians busking on a nameless city corner are harassed by the local constabulary, and meet some other targeted musicians en route to court — leading to a supergroup! The only episode to feature the character JERRY onscreen, though he appears as a voice-only role from offscreen occasionally in later episodes. ANTHONY BARILLA guest stars as a musician’s rights activist.
1.02 “Shy One Girl” When DEBRA goes missing under mysterious circumstances, the gang must rescue her or lose their gig playing a live score to Harold Lloyd’s 1924 film “Girl Shy.” Peter Falk cameos, but not “in character” due to rights issues.
1.03 “Two Bass Hit” CHRIS has trouble when his upright bass is wrongfully accused of assault. Clearly the nadir of the (available) episodes, the thin plot’s issues are compounded by a offensively casual treatment of the underlying crime. Rumor has it this script was retooled from a completely different property, but no real details are available. BARILLA appears again, but this time as a prosecutor, which is jarring given that both characters play the accordion.
1.04 “Sins You Been Gone” During a workshop for a new work based on the Seven Deadly Sins, MARGARET discovers her cello can open a portal to hell, but only if out of tune in one specific way. ANDREW SHUE, later of “Melrose Place,” guest stars as an inexplicably upbeat and bumbling Satan obsessed with Beanie Babies.
1.05 “Titus Gone Mad!” Attempting to cram the plot of Titus Andronicus into a 22-minute sitcom proved a worse misstep than episode 3,. Deprived of creative control, the stars were prisoners of their contract and give it a try (though the knowing looks from JOHN and CATHY make it clear they’re not happy), but the resulting mess marks the point when the network started getting cold feet. Ironically, the soundtrack here proved one of the groups’ bigger hits at the time, and has eclipsed the memory of the episode entirely. Paulie Shore guest stars as Titus.
1.06 “Man or Muppet?” After a confusing altercation at an east side diner, KIRK is transformed into a muppet by a disgruntled waitress who dabbles in the occult (Fairuza Balk). The gang seeks reconciliation with her coven, but KIRK isn’t entirely UNHAPPY as a thinly-veiled analog of Henson’s Animal.
Man, what I wouldn’t give for a print of the Halloween, variety-show-style special!
The least surprising words in this article are “Caswell” and “Dallas”
A Dallas-based restaurant group is opening a “female-forward” joint called Postcript over in River Oaks. It’s very, uh, pink.
However, there’s something a bit odd about the management of this joint:
PostScript has been touted by its Dallas-based hospitality group GAP Concepts as “female-forward,” which the restaurant is demonstrating by boasting a very pink interior, paintings of butterflies, a see-and-be-seen area called the “Princess Table” and a button that summons champagne to a guest’s table.
With that in mind, GAP Concepts is led by Veeral Rathod and Obi Ibeto, both men. They tapped two men—noted Houston chefs Bryan Caswell and JD Woodward—to run the kitchen. Jeb Stuart, also a man and the former general manager of Coltivare, is overseeing the wine program, and fellow men Mike Sauceda and Steven Ripley will serve as bar manager and general manager, respectively.
Huh.
The point, just to bring it home, is this is a restaurant designed for women with a very male leadership team. When asked about this, a representative for PostScript said the restaurant “has a well-balanced team across all positions with diverse talents. Right now, they are actively building up the senior leadership, specifically seeking awesome female perspectives.”
Uh-huh. Just not, apparently, in any of the actual leadership roles.